Token Theft Vs Password Theft How Attackers Bypass Mfa Token Theft Vs Password Theft How Attackers Bypass Mfa
Net Worth Profile Overview
Token Theft Vs Password Theft How Attackers Bypass Mfa Token Theft Vs Password Theft How Attackers Bypass Mfa Net Worth & Biography

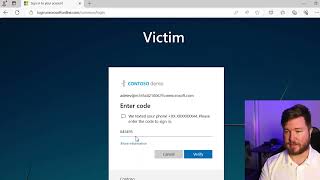
Want to uncover the latest insights on ransomware, dark web threats, and AI risks? Read the 2024 Threat Intelligence Index ... Adversary-in-the-Middle (AitM) attacks are one of the most dangerous ways threat actors Phishing attacks are evolving, and even multi-factor authentication ( Ever stay logged into a SaaS app “for convenience”? That small habit could give Multi-factor authentication raises the cost of account compromise. It does not make verification unbypassable — and the reason it ... In this video, I break down how Adversary-in-the-Middle (AiTM) phishing attacks
Big thank you to ThreatLocker for sponsoring my trip to ZTW25 and also for sponsoring this video. To start your free trial with ... Do you trust AI to summarize e-mails and automate tasks for you? Well, be careful. Get the FREE report here: ... How Hackers Bypass OTP to Login/Register in any website 😱 You need to Know this🫣
Estimated Worth: $73M - $110M
Salary & Income Sources

Career Highlights & Achievements
Assets, Properties & Investments
This section covers known assets, real estate holdings, luxury vehicles, and investment portfolios. Data is compiled from public records, financial disclosures, and verified media reports.
Last Updated: May 16, 2026
Net Worth Outlook & Future Earnings

Disclaimer: Disclaimer: Net Worth estimates are based on publicly available data, media reports, and financial analysis. Actual numbers may vary.











